WordPress Hack i2wp.org – How To Fix
WordPress Hack i2wp.org – How To Fix
I recently brought on a new client who’s WordPress based site had been neglected. As is typically the result, the site became compromised and their Google Adwords campaigns had been suspended and their site blacklisted. They were looking for guidance ASAP.
I began my normal process of combing through source code and running a couple scans on the file system. Nothing seemed to catch my eye. Luckily, there is another great source called File Viewer that saved the day. File Viewer allows you to view the source code of your site based on the referrer and the user agent you would like to use.
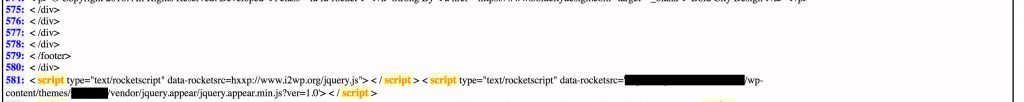
After doing a search on File Viewer and examining the source code with Google as the referrer and Firefox as the User agent, it was evident that an extra script had been added in the footer: i2wp.org/jquery.js. Got ya!
In the end, the site was compromised due to a plugin that had not been updated in some time. Running my necessary scans, closing backdoors, and replacing all plugin and WordPress core files did the trick.
I’m happy to report that all Adwords campaigns are back running and the site has been removed from all blacklists. Hope this helps somebody in a similar situation.






Share Your Thoughts